Application access#
Business system#
Before starting to access,To figure out the general situation of the company's business system:
- What systems are there
- All systems are supported by what protocols are supported by single -point login or unified accounts
- There are several users' data sources,What are the retention and abandonment
- What is the synchronization relationship between data sources
etc.
system structure#
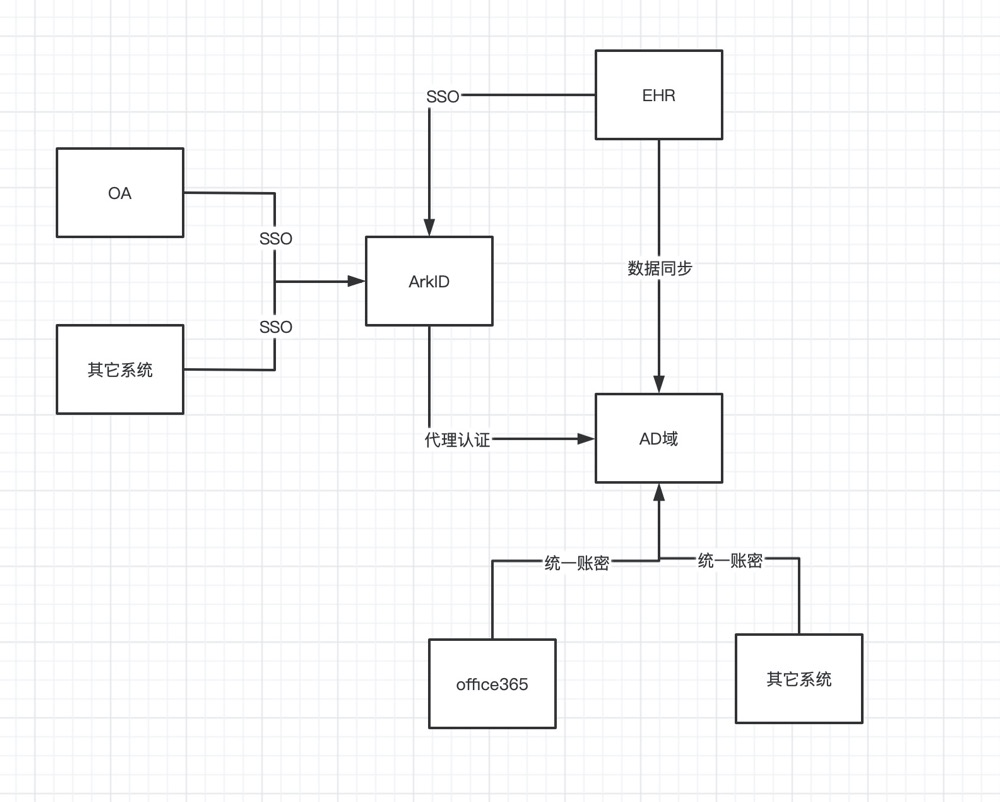
After dealing with these problems,You can start designing the system architecture,The figure below shows a typical system architecture diagram example:
After the user data enters the EHR system,Synchronize to AD domain via SCIM data,Use AD domain as the standard data source,Microsoft systems or systems that support ADs can directly connect with AD domain(Notice,AD domain is a unified account dense,Not single -point login),Other systems such as OA can be connected to ARKID through single -point login protocols such as OIDC or SAML2。
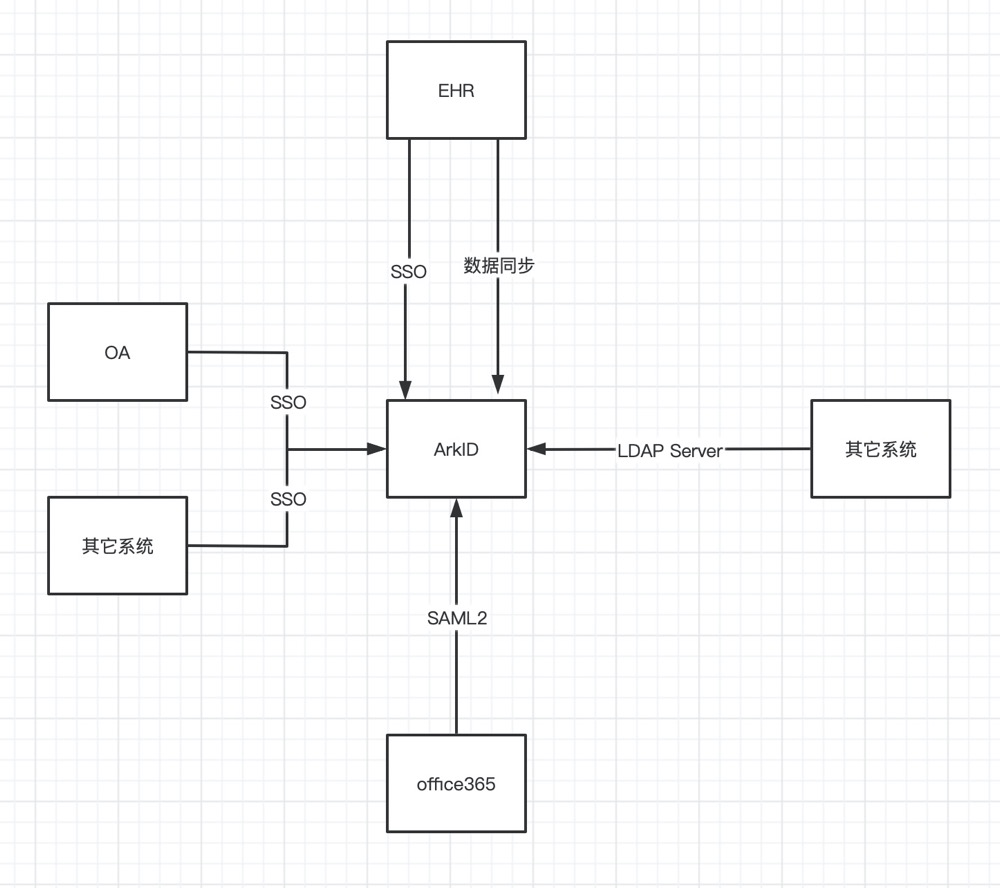
There can also be another architecture design,As shown in the figure:
In this architecture,Arkid can be used as LDAP Server provides unified account secret services outside,The system that has supported AD domain can be directly accessible。Such as flying books,Three -party systems such as Office365 can be accepted through the SAML2 protocol to complete the single point login。
Application access#
sign in#
ArkID Support for different protocols,So as to support a variety of single -point login protocols
Unified authority#
In addition to the inlet authority that can be controlled by a single point and corresponding to the single -point login,Arkid also provides a technical solution for uniformly controlling permissions in the application。
Unified approval#
ArkIDProvides all technical solutions for all requests that need to be approved within the application,And support these approval requests to push to different approval systems。